A Comprehensive Guide to Security Testing for Manual Testers
As the world becomes more reliant on technology, security testing has become an increasingly important aspect of software development. While automated tools can be used to assist with security testing, manual testers play a crucial role in identifying vulnerabilities without having specialisation in security testing tools.
In this article, we will provide a comprehensive guide for manual testers on how to conduct effective security testing.
But before going into more detail, lets take a closer look at why doing security testing manually is necessary.
Necessity Of Manual Security Testing:
Despite the rapid advancements in automation technology, there are certain aspects of web security testing that still require human attention to detect potential vulnerabilities within an application. For instance, vulnerabilities such as business logic issues or cryptographic issues need a manual verification process.
This is why conducting security testing manually is essential. Manual testers often use a combination of handpicked tools and software that are best suited for evaluating their specific application requirements. These may include customized scripts and automated scanning tools.
Advanced techniques used by manual security testers involve precise test cases such as checking user controls, evaluating encryption capabilities and performing thorough analysis to discover nested vulnerabilities within an application.
It’s worth noting that manual security testing does not rule out the use of automation altogether. In fact, experts can leverage automation technology to find patterns or other clues that might uncover important information about the application’s vulnerabilities.
The main objective of manual security testing is to identify weaknesses and potential vulnerabilities in an application which may not be completely revealed through automated means alone.
Therefore regardless of how many automated testing software one might use, it remains critical for analysts to manually analyze software behavior in order ensure its integrity while maintaining confidentiality and availability principles at all times.
Here are some techniques that are effective and efficient to do security testing manually:
Monitor Access Control Management:
This involves testing if only authorized users have access to restricted areas or functions within the application. For example, a manual tester could try accessing pages that are intended only for administrators by entering the URL directly into the browser.
Access control management can be categorized into two parts:
- Authentication – Who are you?
- Authorization – What can you do and what information do you have access to?
Dynamic Analysis (Penetration Testing):
Penetration testing is an advanced form of security testing that attempts to exploit vulnerabilities in a system using tools and techniques similar to those used by attackers. For instance , conducting penetration tests on web applications by trying SQL injection attacks or Cross-site scripting (XSS) attacks .
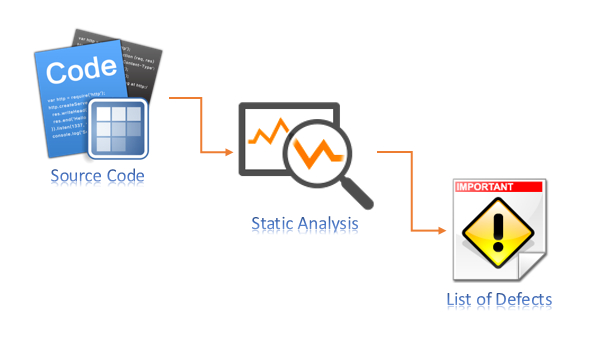
Static Analysis (Static Code Analysis):
Another popular method of manual security testing is static code analysis. Static code analysis refers to analyzing source code without executing it . It helps detect defects before they become vulnerabilities during runtime .
An example would be scanning source code with automated tools like SonarQube which checks for coding standards violations, security issues etc.
The purpose and scope of static analysis tools can vary significantly, ranging from enforcing code styling to performing compiler-level checks for logical errors, among other things.
In essence, static code analysis helps ensure secure coding without the need to execute the actual code.
Check Server Access Controls:
Web applications provide multiple access points for users to perform their tasks, but it is imperative to maintain security measures that prevent data breaches or cyber attacks.
So how can testers ensure the effectiveness of server access controls?
Manual testers should verify server access controls such as user authentication mechanisms, password policies and other authorization methods being used correctly in order prevent unauthorized access from external sources.
To check whether an open access point has been sufficiently secured, manual testers must attempt accessing these points from various trusted as well as untrusted machines with different IP addresses. In addition, a variety of real-time transactions should be executed in bulk volume to test the application’s performance under load conditions.
While conducting security tests manually ,the tester should also examine if any open-access points within the application allow specific actions by users in a secure manner. For instance , testing uploading files exceeding maximum file size limit or trying restricted file types etc would help identify potential weaknesses
The objective behind checking server access controls is ensuring that while end-users are able to use web-based applications seamlessly, they remain protected against possible vulnerabilities and exploits originating from malicious sources .
Session Management:
Manual testers need to test session management capabilities of target systems which includes checking whether sessions can be hijacked or stolen easily through cookies/session IDs, timeouts work properly etc
Password Management :
Passwords are often vulnerable points in any system so manual testers must ensure passwords meet complexity requirements specified by client i.e length , special characters used etc along with password hashing & salting best practices .
How can one verify the effectiveness of password management?
In cases where web applications or systems do not enforce strict password policies, such as requiring numerals, special characters, or passphrases, passwords may be easily guessed through brute force attacks that allow unauthorized access to user accounts.
Moreover, if passwords are not stored in an encrypted format , they become more vulnerable and susceptible to being stolen. Attackers could use various methods like SQL injection to penetrate databases and extract sensitive information.
Even when passwords are stored in a hashed format , once retrieved by attackers they can still be cracked using tools like Brutus,RainbowCrack among others .
Therefore it is essential for manual testers to check whether these security measures have been put in place correctly within the application during testing phase.
Brute-Force Attacks :
Brute-force attacks involve repeatedly guessing a username/password combination until valid credentials are found . Manual testers must test applications against brute force login attempts using various combinations of usernames and passwords
SQL Injection:
SQL Injection is one most common type of attack where malicious inputs entered into input fields cause unintended database queries resulting in data breaches.
So how can we prevent SQL injection attacks?
Manual testers must check all input fields thoroughly including search bars, form fields etc to prevent SQL injection attacks.
For instance, manual testers may enter single quotes (‘) in an input field to verify whether the application accepts them. If the system returns a database error message, it indicates that user input has been inserted into some query sent directly to the database and executed.
Such errors could lead attackers to crash entire applications or extract sensitive data like usernames, passwords and credit card numbers. Hence it’s important for security testing teams ensure proper measures are taken during development phase itself so as not expose applications against this type of vulnerability .
Cross-Site Scripting:
Cross-site scripting (XSS) is another common type of attack where malicious scripts are injected into web pages.
The most common types of XSS are:
- Reflected XSS, when script executes immediately (in search suggestions or by following a link with XSS in URL);
- Stored XSS, when script saves (as a user’s comment) and executes when another user opens the page.
Manual testers should test for XSS by entering HTML tags or script codes in input fields to check whether the application sanitizes and validates user inputs properly.
These malicious scripts can perform various functions such as stealing login credentials or session tokens, logging keystrokes, or executing arbitrary actions on behalf of the user.
Manual testers must ensure that input fields do not blindly trust unvalidated user inputs and should encode output from these fields appropriately if they are included in server responses.
To protect against XSS attacks, proper input and output encoding techniques should be implemented during application development. This helps prevent attackers from injecting harmful scripts into web pages which could lead to sensitive data being compromised.
URL Manipulation :
URL manipulation involves tampering with parameters in a URL query string to bypass security measures .Manual testers should try manipulating URLs by altering values in parameter fields to see if this results in any unexpected behavior from target systems.
Manual testers need to verify whether the application allows sensitive information in the query string, especially when using HTTP GET method to transfer data between server and client.
When an input is given via URL, it passes this information through parameters present in the query string. Manual testers could change parameter values in the query string to check if such modifications are accepted by servers .
Sensitive user information may be passed through HTTP GET requests while fetching or requesting data. If manual testers can manipulate these variables passed via GET request ,they may gain unauthorized access to confidential user data.
It is therefore important that security testing teams ensure all inputs received via URLs are properly validated and sanitized during development phase itself . This will help prevent exploitation of possible loopholes later on during production use cases.
CSP (Content Security Policy):
Content Security Policy headers can be used to mitigate various types of attacks including cross-site scripting , clickjacking, code injection etc.Manual testers need ensure that CSP policies are implemented correctly within applications being tested .
CORS (Cross-Origin Resource Sharing):
CORS allows resources on one domain/origin accessable from another origin/domain but also opens up risks like CSRF .Manual Testers must verify if CORS mechanisms have been implemented securely without opening doors for attackers
CSRF (Cross-Site Request Forgery):
CSRF is an attack where user performs unwanted actions on website they’re authenticated on behalf of attacker who has tricked them into clicking link/button. Manual testers need to confirm that anti-CSRF tokens are present & working as expected .
Open Redirect:
Open redirect vulnerabilities allow attackers to redirect users visiting a legitimate site onto other malicious sites.Manual testers must check all redirects thoroughly and validate redirection targets before allowing them through.
Automated security testing is useful, but it’s not enough to guarantee that a web application is completely secure.
To make sure the application has no weaknesses or vulnerabilities that could be exploited by attackers, businesses must also conduct manual security tests. These types of tests can detect issues that automated tools may miss.
Manual testing can help identify problems like injection vulnerabilities and other flaws in how the application works which automated methods might not catch.
If you’re planning to test your web application for security risks, consider using these effective manual techniques during your testing process.